Email Security and Authentication
The government mandated a strict DMARC policy for .gov domains. How did they do?
minute read
In October 2017, the Department of Homeland Security issued Binding Operational Directive 18-01 focused on securing the email and web traffic of the United States federal government. The highlights of this directive include enabling StartTLS to encrypt email traffic between networks, implementing email authentication standards for .gov domains (including SPF, DKIM, and DMARC at p=reject), and moving all sites to secure “https” URLs.
BOD 18-01:
“Within one year (October 16, 2018) of BOD issuance, set a DMARC policy of “reject” for all second-level domains and mail-sending hosts.“
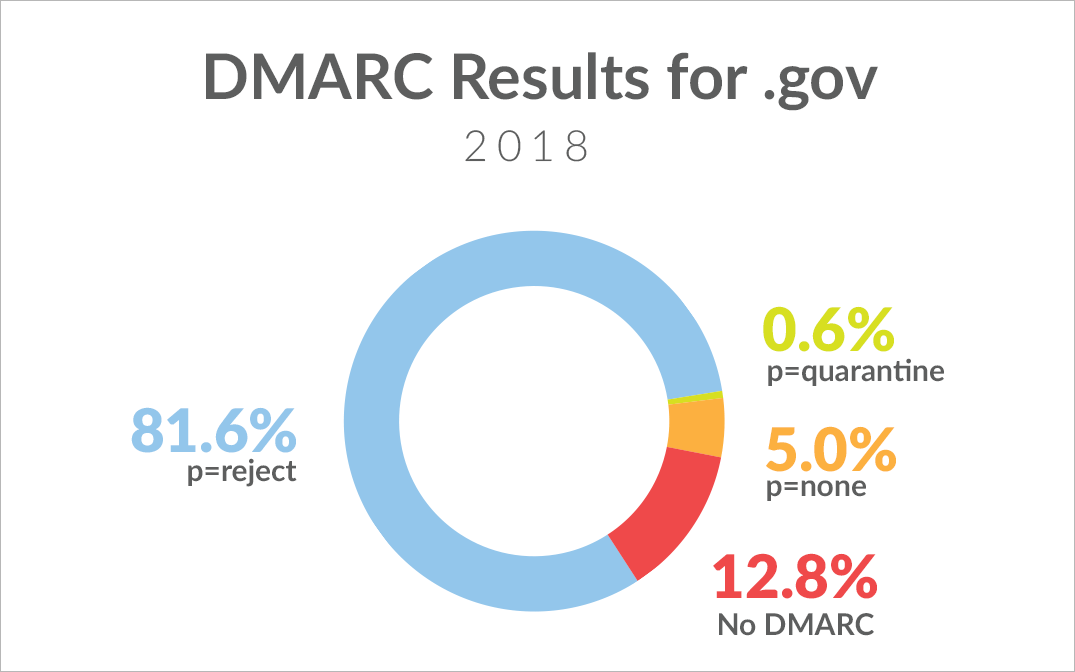
On November 1, 2018, two weeks after the DHS deadline to be at p=reject, we looked at 1000 .gov domains. We’re happy to report over the course of the last year, the government was hard at work getting their email world in order, with 81.6% of .gov domains surveyed achieving the required p=reject policy. Unfortunately, a handful of .gov’s are still at the p=none (5%) or p=quarantine (.6%) stage, and a shocking 12.8% are still not publishing a policy at all.
While the directive doesn’t list any punitive actions imposed against a .gov domain failing to implement p=reject, there are still a few domains needing to pull up the bootstraps and get this implemented correctly.
DMARC Results:
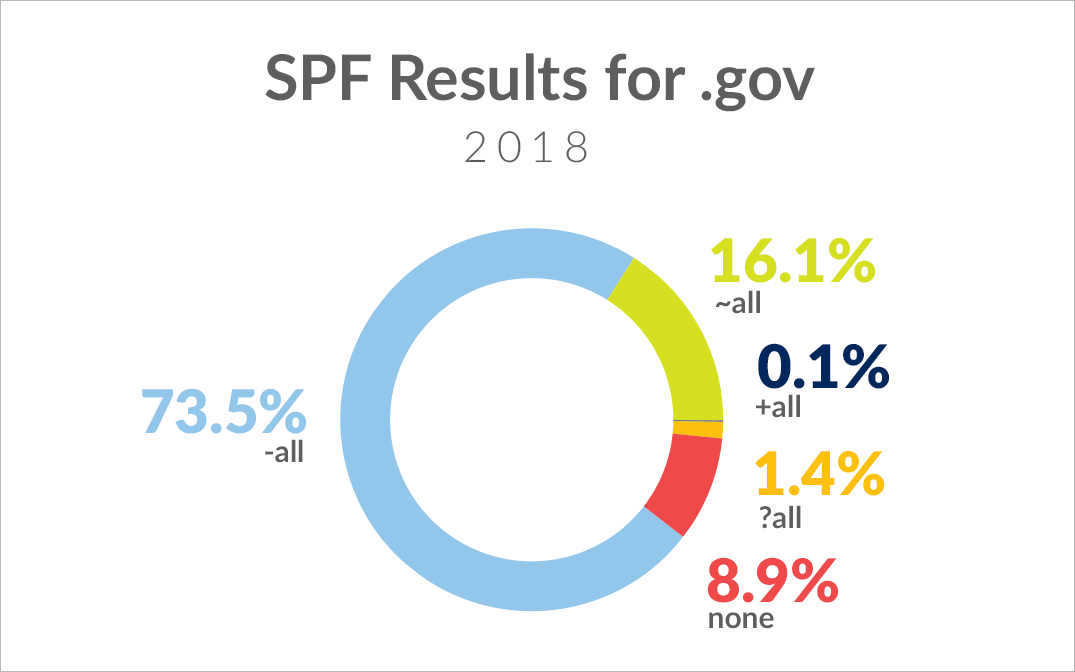
The government shouldn’t stop there, either. We also looked into the SPF policies of these same domains for a different look into email authentication. The vast majority of domains have their SPF set to -all (73.5%), followed by ~all (16.1%), ?all (1.4%), no record (8.9%), and even one domain with +all (.1%). There is definitely additional room for improvement in publishing a valid SPF record for these domains. Don’t forget: Poor SPF and DKIM authentication can have a significant impact on deliverability.
SPF Results:
While the US government set the pace for adoption of DMARC in the marketplace, even a binding directive leaves room for improvement toward total adoption. Hopefully with the government’s successful example, adoption across other industries and verticals will follow suit, driving adoption and increased authentication efforts. After all, with nonprofits’ nearly 94% non-adoption rate and law firms leading our studied industries with only 38% of firms using DMARC, there’s a lot of room for improvement out there.
If you have questions about DMARC or how your DMARC configuration is working, reach out to us. We have a team of experts ready to help.