What is DKIM authentication?
What exactly is DKIM in email? DomainKeys Identified Mail (DKIM) is a core email authentication standard necessary to keep your email safe. It was designed to fill some of the gaps Sender Policy Framework (SPF) authentication cannot fill. Plus, without a created DKIM record, you won’t be able to fully benefit from Domain-based Message Authentication, Reporting, and Conformance (DMARC), a stricter standard available.
However, DKIM can be the most complicated standard to configure and implement.
DKIM helps organizations claim responsibility for sending messages in a way that is verifiable by mailbox providers (MBPs). To do so, there needs to be cryptographic authentication. Creating the record and the associated keys takes some skill.
Why is a DKIM record important?
Once you understand what a DKIM record is, it’s easier to recognize its value. You can think of a DKIM record as a one-of-a-kind signature assigned to your domain that sits within a message’s header. Email servers see that a message is trying to be sent, and the technology looks for this digital signature as proof the content is coming from the domain claiming ownership of the message.
When working in tandem with SPF, DKIM better protects your brand from spoofing incidents, ensuring any email sent to your subscribers is actually from you or your business—and not from an imposter. DKIM authentication helps mailbox providers detect forged sender addresses, which is critical in stopping cybercriminals from obtaining sensitive information from your company and the recipients on your email list.
Businesses that neglect to implement DKIM measures leave themselves vulnerable to bad actors impersonating them. These bad actors can alter the address a message appears to come from. To the untrained eye, fake messages may appear real—especially when they are filled with your brand logos, graphics, and statements.
Email DKIM signatures are significant in the message delivery process. Verifying email service providers can identify your domain and recognize when content is from you helps messages end up in primary inboxes, where recipients are more likely to see them.
Companies skipping out on DKIM in email take a more lenient approach to security, which may result in messages being delivered to spam or junk folders. Additionally, outlets like Gmail and Outlook now alert users when they are unable to recognize a bulk sender as legitimate due to a DKIM failure.
For bulk senders, DKIM is now a minimum requirement for deliverability at Gmail and Yahoo—so senders who do not currently have it in place should act quickly. Incorporating DKIM in email takes your company’s security measures to a new level, increasing your chances of stopping outside parties from interfering with customer trust in your brand.
How does DKIM work?
You can use DKIM to keep your email safe through several steps:
1. Creation and use of the key pair
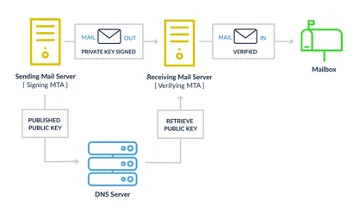
To use DKIM for your business, you, the primary domain owner, must generate a cryptographic key pair comprising one private component and one public component. From there, you need to position the public key within your domain’s Domain Name System (DNS) record. Note that the public key should be included as a TXT record for it to work correctly.
Your business then needs to create a header and selector for the authentication process. A private key is used by the email server sending the message to create a unique DKIM signature that is added to the message as a special header. The header contains a domain and a selector, and all will be considered for the authentication process.
The selector allows ESPs or systems (s=) to send DKIM-signed emails using the same domain (d=). The receiving email servers leverage the DKIM signature in the message headers to authenticate that the message was created by the sender and that it hadn’t changed from the moment it was signed to when it was received—which can otherwise happen when a message is auto-forwarded.
2. DKIM Email encryption and signing
As the domain owner, you will draft a message to send and the email platform you use to write the message encrypts select inputs. Your email will not be encrypted, but the DKIM signature will use encryptions and elements within the message to create the signature. This is known as email hashing, and it incorporates a specific code into the header of an email.
The recipient’s email server recomputes the encrypted hash according to the message’s contents. At this time, the public key that exists within the DNS is used to check the message.
2. Email encryption and signing
For an email to pass the DKIM authentication stage, the hash value noted by the server on the recipient’s end must match the information found within the encrypted email header. Email servers perform this test to determine whether a message has been altered since it was first signed. The individual reading the email can see the precise domain and selector from which the email originated.
How to set up DKIM
This is where DKIM can become a challenge. There are several steps to creating the record and then publishing the record to the DNS, so you may want to get help from your IT department or email service provider (ESP).
Inventory your sending domains
This is an important but often overlooked step. It might seem fine to assume the only sending domain necessary to protect is the one from which you’re sending either the most mail or your marketing mail. However, there can be several other places from which emails are generated. Make sure you have a list of every sending domain, including vendors sending mail on behalf of your domains, like those for customer service.
Use an ESP to provide DNS records
An ESP determines which elements of the email to include in the signing process. The header must be represented as a signature for DKIM to work. Additionally, the message elements selected by an ESP cannot change from this moment forward.
Without clarification, the receiving server won’t know what to check to ensure nothing was manipulated in transit. In most cases, all you need to do is publish the public key in your DNS records for an ESP to complete this process for you.
Extra tip:
The elements included in the DKIM signing process must remain unchanged in transit or the DKIM signature will fail authentication.
Encrypt
The core of the DKIM mechanism is encryption. Your encryption needs to be configured specifically for your server, and your email service provider (ESP) should be able to help you install a DKIM package tailored to that server.
Once enabled, the platform will automatically create a “hash” of the predetermined signature elements. This will convert readable text into a textual string of numbers and letters. This string is unique to your server.
While this code may seem like a group of random characters, email platforms carefully select a unique chain to be decrypted later using public keys. Most encrypted emails are converted into strings of text containing 32, 40, or 64 characters to heighten security.
The encryption process is hard to tamper with once a message is sent. This process gives your brand an extra layer of protection from outside parties who want to pretend to be you or manipulate headers and body content before it gets to a recipient.
Key creation
As previously mentioned, the DomainKeys in DKIM include a public key published on the DNS record as well as a private key, which is included in an email’s header.
- Private: The hash string exists, so now it needs to be encrypted with a private key. This private key gets assigned to a unique combination of domain and selector. Since it is unique, you can have several legitimate private keys for an individual domain. The ESP provides the private key and limits who has access to it. It is unlikely you or marketers will ever need to see the private key.
- Public: The public key is the only match for the private key in the email signature. The key pair match enables the email provider to decrypt the DKIM signature back to the original hash string for authentication.
Publish your public key
You’ll also need a selector record. This will include the DKIM subdomain storing the public key. The public key will be included in the TXT record of your domain, which should be published on the DNS.
Publishing a public key takes little time, even if you are new to the process and want to optimize security for your email marketing campaigns. Only public keys should be shared. As the name implies, private keys keep your messages safe from malicious activity.
DKIM signatures
A special header is used in each message configured with DKIM. This is the DKIM signature. Within it is information about the sender, message, and location of the public key used for email verification. This header is required by all MBPs using DKIM to confirm your identity.
Tags
The DKIM header includes several necessary components represented by using tag=value pairs. The tag will include a single letter and an equal sign, which indicates which piece of information it represents—sender, message, and public key location.
ESPs provide a number of available tags, but some are required where others are not. If a required tag is missed, you’ll get a verification error from the MBP. However, if an optional tag is disregarded in your DKIM header, you won’t fail authentication.
Tags without values are treated as such—valueless. If you do not include a tag in your DKIM signature, like an optional tag, the MBP will assume its default value.
Required tags
There are quite a few required tags. DKIM signatures without these tags will result in an error.
- v= is the version of the signature specification. This should always be one.
- a= indicates the algorithm used to create the DKIM signature.
- s= indicates the selector record name used with the domain to locate the public key in DNS. The sender creates this with a letter or number, there is no specific required value.
- h= is the entire list of headers used in the signing algorithm to create the hash in the b= tag. The order of the headers in the h= tag is the order in which they were presented during DKIM signing. This is also the order they should be presented when being verified. The value is the list of header fields which should not change or be removed during message transmission.
- b= is the actual DKIM signature of headers and body of the mail message.
- bh= is the computed hash of the message body. If you choose to add the body of your email in the header, this is the string of characters representing the hash created by the hash algorithm.
- d= indicates the domain used with the selector record (s=) to locate the public key. The value is the sender’s owned domain.
Sending a signed DKIM message
Once the encryption key is created and configured at the email-sending server, the message can be sent with the protection of DKIM. If you’ve set everything up appropriately, DKIM authentication should work as intended. There isn’t anything you need to do to facilitate its deployment, but your ESP should be able to provide more specific directions.
After you deploy the message, there are several things happening as the email approaches the receiving server for delivery.
Verifying a signed DKIM message
As the mail is in transit, the receiver will see it has a DKIM signature. The signature reveals the combination of the domain and selector signed during encryption. It will need to validate the DKIM signature generated using the private key, so the receiving email provider then runs a DNS query to obtain the public key.
The public key is used to recompute the hash of the message being received. Then, it compares with the signature that came with the message that was signed with the private key. If these hashes match, then DKIM passes.
If it is a match, the receiving server can trust the message wasn’t manipulated in transit because had it been, the hashes wouldn’t match. The DKIM match provides confidence the message isn’t spoofed.
How does DKIM prevent domain spoofing?
Any manipulation of the encrypted keys will indicate something wrong in transit. Since mailbox providers generally will not allow the delivery of a DKIM failure, you’re more protected against phishing, which typically relies on a spoofed domain.
Creating a unique digital signature and including it with your message’s header leaves less room for imposters to target your recipients, as DKIM makes it much harder to spoof the domain. Both your Dsignature containing a private key and the encrypted email are compared before final delivery.
DKIM also allows senders to inform receiving servers of their legitimate emails being sent—which are the messages with DKIM measures in place. You have your own digital signature, the public key associated with your company is pulled from the DNS records, there is a verification of your DKIM signature, and all encrypted information surrounding your content is checked for authentication.
Since DKIM is now a minimum requirement from major ESPs, receiving servers will be able to filter out messages that do not sign using the DKIM approach.
Use an email marketing tool to gauge campaign performance.
Validity® Everest is the ultimate tool for increasing email engagement and protecting your domain. Trusted by more than 10,000 digital marketers, Everest provides the information necessary to enhance delivery rates, discover what resonates with your audience, and free your promotional content from spam channels.
We enable you to have the visibility to make adjustments so that you can get messages to more people efficiently. Maintaining trust with your customers and grabbing the attention of viewers is possible with this tool, which lets you see reports and benchmarks tailored to your company’s domain.
Find out how Validity can transform your email operations for the better.
FAQs
How does DKIM improve deliverability?
With more confidence in the veracity of your email, DKIM is now a minimum requirement for bulk senders with Gmail and Yahoo. With high delivery rates, low spam complaints (because recipients will believe your email to be trustworthy), and a general demonstration of taking security seriously, you’ll reap the positive benefits of DKIM authentication. Combining these signals contributes to a good sender reputation and deliverability.
What do SPF and DMARC have to do with DKIM?
SPF, DKIM, and DMARC work together to protect your domains from spoofing. SPF is the most basic level of authentication and is typically the most common. Since DKIM can be so much more complex than implementing SPF, marketers will frequently stop there. But without the additional protection from DKIM, marketers then lose out on the potential for DMARC, which is the gold standard of email authentication.
How do I add a DKIM record to my domain?
What happens when DKIM fails?
How do I know if DKIM is working?
A comprehensive email performance monitoring tool can help you not only understand your infrastructure, but keep track of it. Validity’s email success platform allows you to see the volume of sent email not passing DKIM authentication. SPF, DKIM, and DMARC can be tracked to illuminate how much mail is being filtered because of failures. If you notice issues, like consistent DKIM failure of all mail, you can troubleshoot right away, rather than waiting for the negative deliverability impact of a damaged reputation.
Is DKIM safe enough?
Having SPF and DKIM properly configured is a key step toward email authentication, but they’re not the last or only steps to take. Once SPF and DKIM are in place, you’re primed to take on DMARC, one of the safest authentication protocols you can use. With only DKIM, you’re leaving the MBP to choose to handle failing mail how it sees fit.
With DMARC, senders specify how the mailbox provider will deal with any failed messages. So, if a message fails DMARC, you can specify it’s returned to you. If a message fails DKIM, it might be placed in spam without you knowing. Without the benefit of detailed insight, you’re on a path to reputation erosion.
Does DKIM give my messages end-to-end encryption?
Discover how Validity can help you set up and monitor proper email authentication to keep your program safe and secure.
