Protecting company and customer data is essential, regardless of your industry. Proper data security management can help you safeguard your company’s data from various security risks and challenges. Learn why data security is important and how you can be proactive about managing your business’s data safety.
What is data security?
Data security is the process and procedures put in place to protect an organization’s data and digital information from unauthorized access, corruption, and distribution through each stage of its lifecycle. Data security encompasses every level of data protection, including:
- Physical security of hardware and software devices
- Digital security of administrative and access controls
- Logical security of software applications
Effective data security strategies are critical protections against data breaches and data loss from cybercriminal activities. With data security comes improved data quality, as your teams know their network is protected and trustworthy. Setting specific data security standards for your company will help defend against potential security risks.
Data security best practices
Each year showcases digital technology that has evolved leaps and bounds to improve businesses’ communication, data management, marketing and sales operations, and customer success. Yet, the digitization and accessibility of work processes also increase security risks as cybersecurity threats evolve and target weak points in an organization’s data security. Due to the increased risks, implementing new practices keeps you well-positioned against future cyber threats.
Ensure your company is aware of and follows some data security best practices, including:
1. Implement strong password protocol.
Your password is one of your first and most effective lines of defense. As a preventative measure, all employees and users should be required to create strong passwords to guard their accounts. It’s also best to have a scheduled period in which users must change their passwords after some time to maintain high security standards and continue protecting their accounts with a strong password.
A strong password should fit the following criteria:
- Doesn’t contain words or phrases
- Must be difficult to guess
- Uses numbers, letters, and symbols
- Contains eight characters or more
- Has not been used previously
2. Use multi-factor authentication.
Multi-factor authentication (MFA) requires users to submit an additional identifying code to access their accounts and systems. It adds a backup protection method that will stop hackers from unauthorized access if they’ve stolen or compromised a password.
MFA is a simple but effective security addition that won’t place too much pressure on the user. Most people have already used MFA in multiple ways, such as swiping a debit card and entering a PIN. For your accounts’ data security, MFA may look like an automated code that gets texted to the user when they enter their password, which they then submit to gain access to their account.
3. Determine what sensitive data is.
Does your company work with, manage, or store personal data and/or sensitive customer data? Your organization must identify and classify each type of data being collected to ensure data privacy. Sensitive data includes but is not limited to:
- Financial information
- Protected health information
- Social security numbers
- Business intelligence data
Your security team should scan your database and classify the data types, which can then be used to determine which users have access to each classification. This will prevent unauthorized users from accessing sensitive information irrelevant to their job or work.
Important note: Ensure only privileged users, such as heads of security, can alter data classifications. Doing so will help prevent other users from changing your company’s data classifications without approval.
4. Clearly define and uphold your data usage policy.
Your organization should have a detailed and accessible data usage policy that dictates the different data access rules, such as:
- Who has access to data?
- What is proper data usage?
- What are the different types of access?
- How is the policy implemented?
Once shared with all users, this policy should be followed closely to ensure best practice data use. This means restricting user access to customer data if needed and deactivating access when relevant. Any policy breaches should be identified and addressed immediately. Requiring all employees and users to follow the data usage policy will help mitigate data security risks. When establishing the policy, ensure the rules meet data security compliance standards so users still adhere to industry regulations and regulatory requirements.
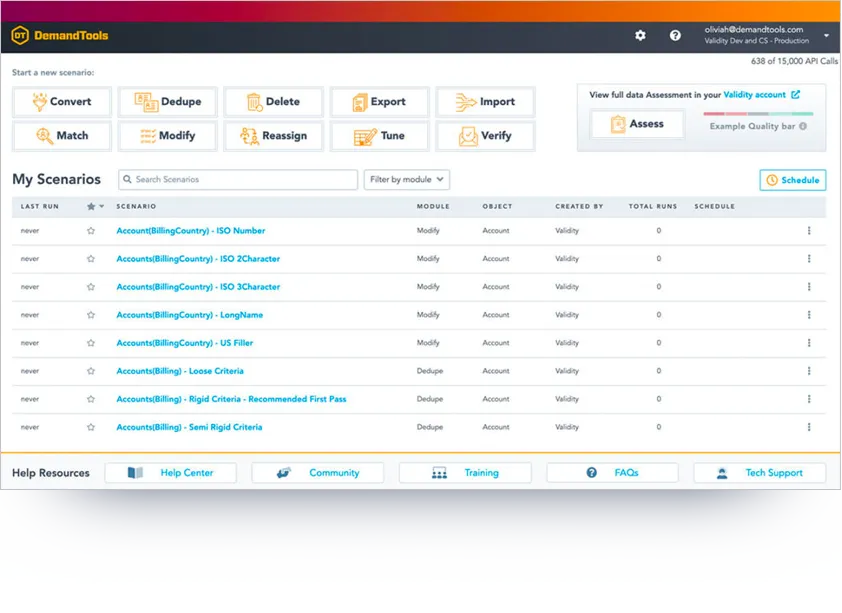
Interested in a secure data management system that keeps data clean and helps implement a data governance process? Discover DemandTools from Validity.
Importance of data security
When companies collect and use data for their business operations, they have a moral and legal obligation to protect their user and customer data from unauthorized access. Much of the digital data stored by organizations contains sensitive financial, personal, or medical information that must be protected. Besides being unethical, unauthorized access or dissemination of this data can have extremely harmful consequences for all parties involved.
Legally, your organization may have to follow statutory privacy requirements, such as the Health Insurance Portability and Accountability Act (HIPAA), the Family Educational Rights and Privacy Act (FERPA), or the Gramm-Leach-Bliley Act (GLBA). The General Data Protection Regulation (GDPR) was enacted in 2018 as a legal framework that companies must follow if they collect and process personal information from any individuals who live in the European Union (EU). This standard protects the data and privacy of EU citizens and holds companies accountable for their data security practices.
If you’re dealing with sensitive data, look into your state, national, and industry legal requirements to ensure you follow proper data security guidelines. Liability and compliance problems can happen if you aren’t properly protecting your data. Although following guidelines can’t guarantee complete compliance, it’s still an effective way to increase your data security and due diligence.
Data security can also improve your organization’s reputation. A data breach will seriously and permanently damage your company’s reputation. Customers and stakeholders may lose trust in your company because their information was compromised in the data breach. Your teams will have to spend time, money, and resources identifying the security gaps and attempting to repair the business’s standing—which may not recover.
Your organization’s information is an invaluable asset, and good data security treats it as such. Effective data protection can give you a competitive edge by limiting competitor access to your information, improving your brand’s integrity, and streamlining data accessibility to users who need it.
Types of data security solutions
There are more solutions and processes you can enact besides using a strong password and multi-factor authentication to combat data security risks. Other ways you can help safeguard data include employing:
Authentication measures
As previously discussed, setting up specific ways to identify and authenticate users before they gain access to your data is critical for data security. This includes setting up measures such as:
- Passwords
- PINs
- Security cards
- Biometrics
Authentication helps company systems know and track who is accessing what and when. It’s a crucial part of data security because companies must be able to track down the root of the problem to fix it. If a data breach occurs because an employee opens an email with malware, the data security team needs to know which employee opened the email so they can get closer to the source.
Access controls
Only certain people in your organization or company should have physical and digital access to various information and data. Implementing measures that only allow users with proper permissions to access data helps protect your organization’s information.
For physical workstations and spaces, this means restricting entry to computers and devices. For digital spaces, it could mean requiring a specific login entry to access a system.
Data masking
Data masking is extremely important when an unauthorized user compromises or accesses data. This security technique involves hiding original data through obfuscation, which makes the information more difficult to read or understand from an outsider’s perspective. Obfuscation may mean the data appears as proxy characters or modified content that looks real but doesn’t contain real information. Only authorized users can see the original data, even with data masking.
Encryption
Almost all organizations should have their communications, files, and databases encrypted to some extent. Encryption uses a computer algorithm to make your information unreadable to unauthorized users. Only if you have proper permissions can you unlock the encryption keys and reach the protected data.
Data security risks
When considering different data security methods, it’s also important to understand what types of risks your organization might encounter:
Accidental exposure
Unlike other security risks, accidental exposure happens when an employee or user shares, loses, or mishandles sensitive data. Often, this is due to an accident or a lack of data security policy training. When someone leaves data open to unauthorized users, they could copy or use the information for malicious purposes.
Phishing and other social engineering attacks
These types of cyberattacks are socially engineered to access and use private information for harmful purposes. Usually, they have been designed to look like they’re from a trusted source to gain the victim’s trust. They then ask for sensitive information or send a malicious link, which gives them access to your data network if the user replies with the details or clicks the link.
To combat phishing and other social engineering attacks, users must understand the importance of checking the email source and looking for inconsistencies throughout the email. If the sender’s email address looks odd, it likely is a phishing scam.
Ransomware
Ransomware is malware that attacks corporate devices and networks to encrypt data from your organization, effectively taking it hostage. The malware may display a message requesting payment for data access, but that can become an additional scam. Companies may choose to pay, but then still lose important data.
This is a particularly harmful data security risk as it can spread rapidly and cause significant data loss for companies. Maintaining regular data security checks, updates, and training and installing anti-malware applications across the company system can help keep employees and users proactive in their data security practices.
Insider threats
Data security risks can also appear as insider threats. Three types include:
- Non-malicious insider: When an accidental exposure occurs, it is considered a non-malicious insider threat. Your employees don’t intend to cause a security breach, but they do so because they’re not aware of proper data security practices.
- Malicious insider: A malicious insider is a user who is trying to steal data or harm your data network for personal gain. They may use their privileged access to data and information to share, sabotage, or misrepresent your company.
- Compromised insider: Similar to ransomware victims, a compromised insider has had their user access or credentials compromised by a cyber attack. They’re not aware of the breach, and the attacker can pretend to be the user and cause harm.
Data loss in the cloud
As technologies advance, more and more data is moving to the cloud for improved sharing and collaboration. However, this interconnectedness also means that data is more challenging to secure as users access data through personal devices and unsecured networks. Due to this, there are increased risks of losing data and sharing sensitive information with unauthorized users.
How will data security change in the coming years?
As data becomes more important and accessible with evolving technologies, how will your organization protect its most valuable asset, customer relationship management (CRM) data, in the future? Trying to be forward-thinking is a difficult task when it comes to the fast pace of digital upgrades each year. The key is to implement an ever-evolving data security strategy that can be updated and adapted to new threats and risks.
By following market changes and technological innovations, such as AI, you can keep your data security competitive. Using a CRM data cleaning tool, like DemandTools from Validity, can also help you recognize anomalies within your data and who has access to it.
Stay proactive with your data security management.
Implement and maintain data security standards to protect your company’s sensitive information. More security measures allow more opportunities for better data quality and analysis. Validity DemandTools platform gives you access to various tools to help your company have clean data that will benefit business decision-making.
Dig deeper into our data cleaning solutions and see DemandTools from Validity in action!