Email Sender and Domain Reputation
Get Out of the Haus! How to Get Delisted From Spamhaus
minute read

Table of Contents
- What is Spamhaus?
- Help! I’m on the Spamhaus blocklist. What do I do next?
- After getting out of the Haus—Spamhaus aftermath
The most dreaded block listings digital marketers face are from Spamhaus. Even the most sophisticated senders can find themselves on Spamhaus’ block lists.
To avoid major damage to your email program, it’s important to understand how to prevent a listing and how to react if you’re listed by Spamhaus.
What is Spamhaus?
Spamhaus is an international authority on IP and domain reputation, founded in London in 1998. Their mission is to track malicious actors and threats, including spam-like activity, to make the internet safer for users.
Spamhaus produces several block lists and data feeds that mailbox providers use to protect themselves against spam and malicious activity. The organization currently protects over three billion email users’ mailboxes.
Spamhaus distributes seven key DNS-based Block Lists (DNSBLs), including the Spamhaus Block List (SBL), Compromises and Snowshoe Block List (CSS), Exploits Block List (XBL), Policy Block List (PBL), Domain Block List (DBL), Zero Reputation Domain Blocklist (ZRD) and the Hash Block List (HBL).
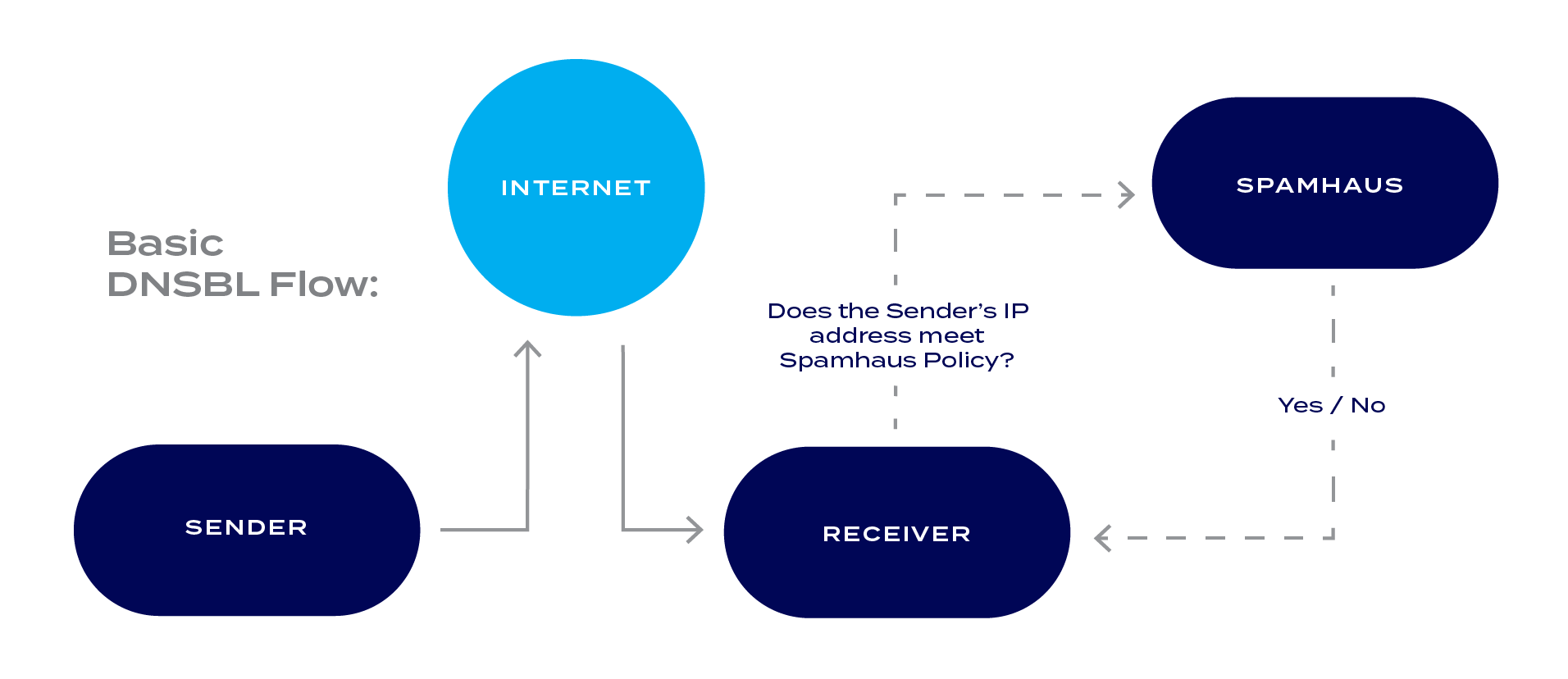
Mailbox providers generally access Spamhaus block lists via DNS in real time to assess inbound messages:
The ZEN Block List groups SBL, SBLCSS, XBL, and PBL lists together.
Most mailbox providers use the combined package of Spamhaus Zen. If you’re listed in Zen, you’ll see a listing for ZEN and for one or more of the included blocklists.
SBL listings are the most common for digital marketers to encounter. Unfortunately, these listings will likely have a high impact on email deliverability. ZEN will identify and reject roughly 85 percent of a typical mail relay’s incoming mail traffic.
To see if you’re on the Spamhaus blocklist, simply check here.
Help! I’m on the Spamhaus Block List. What do I do next?
If you are blocklisted on Spamhaus, you’re probably in total panic mode. This is understandable—the Spamhaus blocklist will affect your deliverability and getting delisted should be your number one priority.
Fortunately, there are a few steps email senders can take to get out of the “Haus” quickly.
1. Take immediate action
First, stop sending mail the second you know you’re listed on Spamhaus. Next, review your most recent email campaigns and see if you did anything differently.
Did you send to a new portion of your sending list? Did you send a new creative? Even simple actions like these might have unexpected consequences.
2. Communicate
It’s important to make everyone involved in your email program aware of your Spamhaus listing. Your technical account manager and email service provider (ESP) are a good place to start. Your technical account manager has experience with Spamhaus, and can either help you delist themselves (see below for details) or point you to someone who can.
Please note that delisting requires you to fix the issue that caused the listing. That’s why it’s important to understand what you might have done differently in your email program leading up to the listing.
3. Fix the issue and proactively monitor your program
If you have trouble deciphering what might have caused the Spamhaus listing, talk with your technical account manager so they can shed light on the situation. Here are a few places to start:
- Review your infrastructure. Ensure your program processes bounces properly and maintains feedback loops. It’s important to promptly remove complainers identified on the feedback loops.
- Review your list acquisition. Identify and stop all high-risk acquisition processes (i.e., list rental and list purchasing). Confirm you’re sending mail only to those who have opted in to your program. Consider implementing a confirmed opt-in permission level for added security.
- Remove inactive subscribers. It’s important to stop sending mail to those who don’t engage with your content. If you don’t already have an inactive suppression policy, implement one as soon as possible. You might also want to try a re-engagement campaign to win back unengaged subscribers. If they don’t engage after such a campaign, delete them permanently from your sending list.
- Proactively monitor. The best way to fix a Spamhaus issue is to make sure it never happens. As you send email campaigns, keep an eye on complaint rates, unknown user rates, and spam trap hits. If you start to see spikes or unusual numbers, involve your technical account manager to remedy the problem before it gets you listed on Spamhaus.
4. Delist and follow through.
Review the delist checklist:
- Confirm your IP’s/domains are listed on Spamhaus.
- Identify what IP’s/domains are affected and stopped sending mail to those impacted.
- Communicate the listing to your technical account manager and email service provider (and ask for assistance if needed).
- Review your recent email sends and look for possible issues that triggered the listing.
- Fix the issues that triggered the listing.
Once you check all prior listings, it’s time to delist from Spamhaus. To delist from Spamhaus, go Spamhaus’ lookup page, then follow the instructions to delist. When you fill out the delist form, be concise. It’s also important to mention you fixed the problems that landed you on the block list.
Remember, Spamhaus has the final authority to decide whether or not to remove you from their block list. Simply delisting doesn’t guarantee your removal.
After getting out of the Haus—Spamhaus aftermath
Congratulations, you’ve been removed from Spamhaus!
This is welcome news. However, the hard work isn’t over. The last thing you want to see is another listing on Spamhaus. This is where proactive account monitoring is key. Make sure you run a healthy email program with good list hygiene practices and no spam-like activity.
In many cases, the best way to achieve full visibility into your email program is with a technology solution like Everest, the email success platform from Validity.
There are many alerts and reports you can set up in the Reputation module of the Everest platform to help you be proactive and avoid future Spamhaus listings.

If you’re concerned about trap hits and blocklistings, reach out to the experts at Validity for assistance.