Domain-based Message Authentication, Reporting, and Conformance (DMARC) is a critical component of a secure email program, helping brands protect their customers, employees, and partners from phishing and spoofing attacks.
Billions of phishing emails are sent daily. DMARC is an essential line of defense for a domain owner against these fraudulent emails. Despite DMARC’s importance, few email marketers know how to effectively use DMARC to improve email security.
To help you strengthen your email security, let’s explore how to get started with DMARC and answer a few common questions about the protocol.
Understanding DMARC
Introduced in 2012, DMARC is one of the most beneficial protocols to be added to the list of email authentication standards. DMARC builds on two email validation protocols—Sender Policy Framework (SPF) and DomainKeys Identified Mail (DKIM). The technology exists to provide greater email security for both senders and email domain owners.
DMARC was first used by businesses in the financial services sector, but it is now recommended for email marketers across all industries. The DMARC email security protocol is supported by all major mailbox providers is supported by all major mailbox providers and is key in protecting email from malicious activity and improving deliverability. Some major mailbox providers (including Gmail and Yahoo) have gone a step further and made a published DMARC record a requirement for bulk senders. Learning how to adopt and implement DMARC demands a complex and multi-tiered approach.
Benefits of DMARC for email
The DMARC email security protocol is the biggest safety check for your email program and is significantly harder for spammers to crack than SPF—which defines which IP addresses are authorized to send mail from your domain—and DKIM—which “signs” your messages in a verifiable way for mailbox providers (MBPs).
Can you confirm that there is no unauthorized mail originating from your domains? With DMARC, you get instant insight into the performance and actual sending activity from your domains. With this protocol in place, you can rest assured that any malicious mail potentially coming from your domain is automatically routed away from your recipients—which helps protect your brand reputation and saves your customers from email attacks.
When you are learning what a DMARC policy is, note the unique benefits below to comprehend how implementation can improve your efforts.
1. Compliance with industry requirements
The industry you work in may call for following regulations relating to email security and authentication procedures. Using DMARC adds an extra level of security to the identity verification process before anything is sent from your domain.
2. Cyberthreat detection
Be the first to know if someone has malicious intent against your brand or customer base. DMARC is effective in decreasing the likelihood of phishing and spoofing attacks, whether someone is using your company’s domain for work or a recipient gets a message from you asking for sensitive information.
3. Authentication for sending messages
Businesses relying on a DMARC policy have maximum visibility over the personnel sending emails from their domains. When configured correctly, DMARC does an excellent job of flagging content deriving from sources trying to impersonate others.
4. Deliverability feedback
DMARC reports provide crucial information about your email ecosystem—including authentication results, domain alignment, potential email threats, and more. Discovering how to read DMARC reports is advantageous for protecting your domain from abuse.
5. Protect domain reputation
Using the DMARC email authentication method is proactive for putting your best foot forward with mailbox providers and your audience. Maintaining control over your email ecosystem increases the chances of only authorized messages reaching users on your email lists. Creating a positive experience with both your domain and brand is a solid way to stay on your recipients’ good side and remain a credible source for original products or services.
How does DMARC work?
At its core, Domain-based Message Authentication, Reporting, and Conformance involves a series of checks to ensure emails are being sent by trustworthy sources—authorized IP addresses. If the email fails its SPF or DKIM check, it is filtered to a spam folder or rejected entirely by mail servers depending on how the DMARC is set up.
The most important elements of DMARC are alignment and reporting. Alignment ensures there is no spoofing of a critical authentication signal—the “header from” address. DMARC domain alignment indicates the “header from” domain name matches the “envelope from” domain, as determined by an SPF check. This is how DMARC builds on the basic security of SPF.
DMARC then verifies if the “header from” domain matches the “d= domain” in the DKIM signature. That’s where DKIM plays a critical role.
A message must pass SPF authentication, prove SPF alignment, pass DKIM authentication, and prove DKIM alignment in order to pass DMARC authentication. If it fails both signals of alignment, the message fails.
Who can use DMARC and how do you get started?
Everyone can—and should—use DMARC. If you’re an email marketer without any authentication standards set up for your mail, you should follow a few steps before using DMARC, including:
- Properly configure both SPF and DKIM. DMARC cannot perform its validation function without these two elements.
- Publish the SPF and DKIM records for your domain.
It will take some up-front work to qualify for DMARC, but it’s an essential way to protect your email program.
What is a DMARC record and what does a DMARC record look like?
DMARC record code relies on tags. These tags provide directions to receiving mail servers about how to treat incoming email. Only two are required:
- v: Version: This identifies the TXT record as DMARC, making it distinguishable from other TXT records. It needs to have a value of “DMARC1” and must be listed as the first tag in the whole record. Without the tag listed first or the value equaling DMARC1, the receiver will ignore it.
- p: Requested Mail Receiver Policy: This is where your policy level matters. Your DMARC record must include a p= value so the receiver knows what actions to take when running the DMARC check. You can have p=none, p=quarantine, or p=reject.
You can also format the DMARC record to protect your top-level, or main domain. Any subdomain you use from there will also be protected. For example, if we send mail from validity.com but we also have a webstore sending email from store.validity.com, a DMARC record to protect validity.com will apply to the store subdomain as well.
If you’d like subdomains to have a different enforcement policy than your top-level domain, you can designate that within the record. For instance, validity.com should be at reject, but store.validity.com should be at none. The record would read “v:DMARC1; p=reject; sp=none” to properly apply the policies. P indicates the primary policy and sp designates the subdomain policy.
Within the record, you can designate where to send your DMARC reports, both aggregate and forensic.
There are several other tags you can use in your record to change default values assumed when the server is checking for DMARC alignment. These do not need to be manipulated, but you can if you want a custom report.
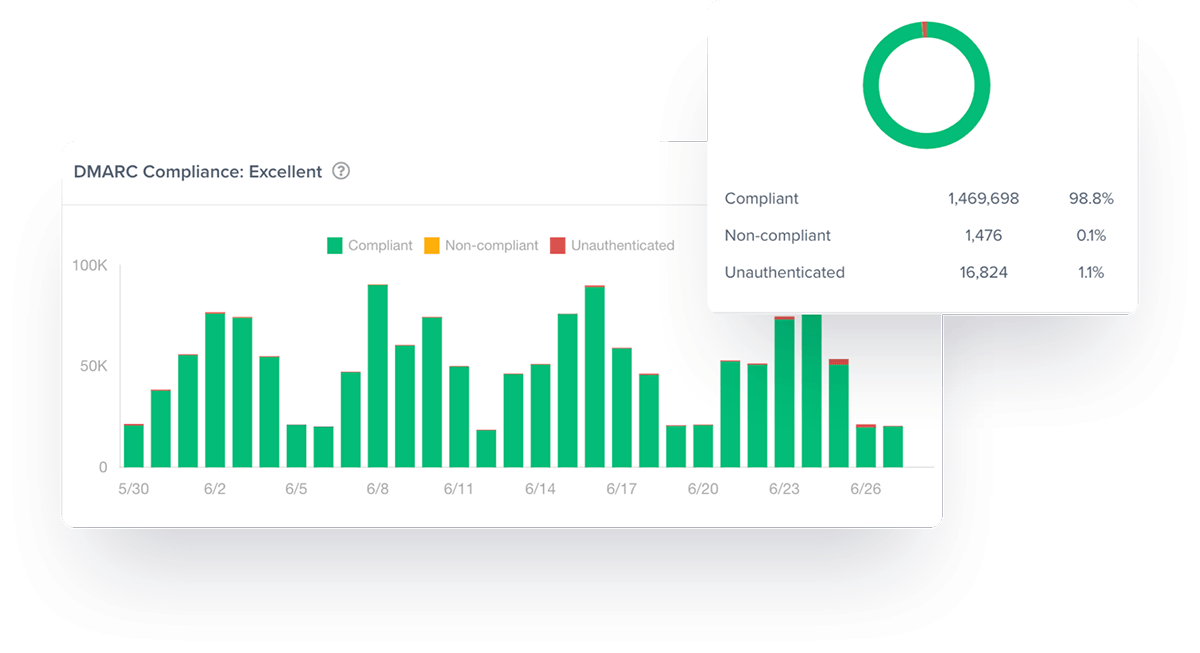
What do DMARC reports look like?
It is integral you know how to interpret the information a DMARC policy will provide. Without the ability to turn insight into action, you’re not using the standard to its fullest potential.
Aggregate reports
These are your daily reports. They’ll show you all the information gleaned from your email deployments. This includes the IPs from which the emails originated, plus your SPF and DKIM results. What you learn from these reports allows you to confirm your legitimate email is being categorized as such and that you’ve got all your appropriate IP addresses authorized.
Forensic reports
You’ll receive a forensic report when an email you send fails SPF and DKIM authentication. Thanks to the added layer of information DMARC provides, you get details about the incident. You’ll see which address it came from and where it went, plus a subject line. You might get the email header, too.
Authentication failure reports can pile up. After you’re comfortable with your aggregate reports, you might want to enable reports only when a spoofed email is detected.
Automate your DMARC reporting with Validity Everest to quickly identify and respond to issues that could cause significant damage.
Automate your DMARC reporting with Validity to quickly identify and respond to issues that could cause significant damage.
Mitigate the impact of spoofing with DMARC
Just because a message fails DMARC doesn’t mean it won’t be delivered. This simply indicates a lack of alignment between SPF and/or DKIM checks.
If you, the domain owner, are receiving and analyzing DMARC reports, you’ll be able to determine how you’d like messages that fail DMARC to be handled. Unless you choose to enforce DMARC, the mailbox provider (MBP) won’t follow the action you outline for emails failing DMARC.
DMARC involves three mail receiver policies:
Monitor policy: p=none
The starter policy for DMARC is one of basic monitoring. Creating a record with p=none enables nothing but the ability to get visibility into DMARC results. You’ll receive daily reports with the information so you can determine how much of the failing mail is legitimate.
Failures can indicate multiple scenarios:
- Your domain might be spoofed
- People within your organization are sending email from your domain without your knowledge
- You have yet to specify a DKIM signature

Using the monitor policy reports that are sent to the domain owner, you can understand your DMARC results and work to resolve any issues.
Many email marketers implement p=none and leave it at that. However, this triggers no action on the receiver’s side. And without providing instruction to the receiving server, you don’t have control over the handling of failed messages or interference in the delivery of malicious mail. This brings us to the next two receiver policies.
Quarantine policy: p=quarantine
You can instruct MBPs to segregate mail failing DMARC from those that don’t. This is a quarantine policy indicated by a p=quarantine in your DMARC record. While you start your DMARC journey with p=none, p=quarantine is the next escalation activity in truly protecting your recipients from harmful communications.
After the receiving server checks the DMARC record to confirm alignment, it will follow the next course of action determined by your policy. With a policy of p=quarantine, mailbox providers will follow your direction and filter the mail into a quarantine or spam folder. This step is essential in keeping phishing and spoofing scams away from your recipients.
Once you implement a p=quarantine policy, you’re at DMARC “enforcement.” This means you’re eligible to use BIMI—an email specification that allows brand logos to display within the inbox of supporting email clients.
Reject policy: p=reject
If you want to provide the fullest protection DMARC can offer, enforce DMARC at its strictest policy level: p=reject. A p=reject policy instructs the MBP to reject the email entirely.
This level means you’ve taken every step available to make your DMARC record work for you. The reject policy allows monitoring for illegitimate or harmful mail by refusing it definitively and reporting back to you on this activity.
The adoption of DMARC itself is relatively scarce, and for marketers using it, few are using it at its full p=reject power.

Troubleshooting DMARC
Alignment
There are several issues you might run into after implementing DMARC. You might see your email placed in the spam folder or rejected by receiving servers consistently.
A smart step in troubleshooting DMARC is to confirm the record is configured properly. If you can verify there are no problems with the record itself, move to analyzing your SPF and DKIM records. Remember, DMARC checks for alignment for both SPF and DKIM.
You should also check your email headers to understand whether or not they’re passing SPF and DKIM. This guide can help you understand how to achieve DMARC compliance and help you ensure alignment in your identifiers.
Deliverability
DMARC can greatly improve your ability to see issues and take appropriate action as quickly as possible. You’ll be more likely to notice a spoofing or phishing incident with DMARC enabled, meaning your email reputation won’t be quietly affected without your knowledge.
You will also benefit from the decrease in incidences of SPF and DKIM failures because only mail coming from your domains can be verified as legitimate on your end. A steady stream of threat-free email is always a win for your email reputation, and your delivery rates should improve along with the trend.
Ensure all emails are received safely
By enabling DMARC in their email marketing strategies, domain owners can better identify and prevent potentially malicious activity and protect their email recipients. However, email deliverability can be affected by a multitude of factors that go beyond Domain-based Message Authentication.
The secret to impressive email marketing campaigns is having the right tools on your side to uncover red flags behind original messages. Validity Everest provides you with the insight you require to get messages to recipients promptly. Thanks to features such as inbox placement insights, sender reputation monitoring tools, and engagement metrics, you can find out why your content is ending up within blocklists or spam folders.
We help you make the adjustments you need to communicate with your audience without unnecessary hurdles. Make informed decisions based on concrete data when you make Validity your partner for email security and assessment tools.
Discover how Validity can help you set up and monitor proper email authentication to keep your program safe and secure.
DMARC FAQ
Do I need DMARC?
Everyone can benefit from DMARC. Unfortunately, the majority of senders don’t use DMARC, which puts not only their brand and sender reputations at risk, but also their email recipients. You’ll know if you have SPF or DKIM failures, but you won’t benefit from the granularity of DMARC reports unless you’ve done the legwork to implement DMARC. Without DMARC, you’re leaving lots of information on the table, and without those insights, your email program could be at risk.
Can I set up DMARC by myself?
Yes! But it can be tricky and often requires professional assistance. You’ll need a high level of confidence in your ability to build.a functional record. You also might need help making sense of the reports you’ll receive or how to solve the issues you’re seeing in them.
If you’re not feeling confident enough to take on DMARC by yourself, there are lots of tools to help you get up and running. For example, Validity’s email success platform can assist you in the set-up, implementation, and interpretation of DMARC.
What if I don’t use DMARC?
There is no penalty. MBPs aren’t treating mail without a DMARC policy associated with it unfairly, but you lack benefits from the additional signals DMARC can send to the receiver. You also put yourself at a greater risk for reputational damage because you could be spoofed unknowingly.
If you have SPF and DKIM set up, it is simple to add DMARC to the mix. However, if you don’t want to add DMARC, you don’t necessarily face a crash-and-burn scenario with your email program.
Does Gmail use DMARC?
Gmail and other email providers, including AOL, Comcast, Hotmail, and Yahoo! Mail, all enable DMARC. You can learn more about DMARC in Gmail using this guide within its help center. And as mentioned, Gmail now requires bulk senders to have a published DMARC record.
Is DMARC free?
DMARC is free. However, you will need to dedicate time and resources to setting up protocols and monitoring your alignment and deliverability. We recommend you adopt an email marketing and deliverability solution like Validity to help your team implement and manage DMARC.
Do I need DKIM if I have DMARC?
DMARC requires you to enable both DKIM and SPF, as it relies on these protocols to know if an email is safe and legitimate.
What is DMARC versus DKIM?
DKIM and DMARC are both security protocols for email, and DMARC relies on both DKIM and SPF to assess if an email is legitimate and, if not, where it should go.
Can DMARC pass if SPF fails?
A message cannot pass DMARC if it fails either SPF or DKIM. This is why DMARC is regarded as the highest level of security for email.