Email Security and Authentication
Gmail’s Blocking Lots of COVID-19 Email. What’s DMARC Got to Do with It?
minute read

*As of May 15, the WHO updated their DMARC policy to reject.*
A recent article on Media Post revealed Gmail is currently blocking roughly 18 million malware and phishing emails related to COVID-19 every day. This is in addition to the 240 million daily COVID-related spam emails Gmail blocks. It shouldn’t surprise anyone that bad actors are exploiting the most significant global crisis in generations for personal gain, but even as a seasoned veteran in the email and email abuse world, the scale of malware, phishing, and other abuse specifically targeting the crisis has truly taken me aback. The email industry’s thus been debating: Does DMARC help or hinder in this situation?
If you’re not sure what DMARC is, that’s no problem. Start here, with a video from our Validity email experts giving an overview of DMARC.
Some people believe Gmail is wrong for blocking mail from places like the World Health Organization (WHO) today. I can recall a recent conversation about whether or not DMARC reject policies will hurt your deliverability with a veteran deliverability/email expert who I respect greatly. Something was said along the lines of, “Publishing a DMARC reject policy could be seen as negligent because it would cause some mail to be rejected.” Suffice it to say, this is not a fringe opinion. It is quite pervasive.
So, if DMARC reject hurts deliverability, why would an organization like the WHO want to put a DMARC reject policy in place? As an entity sending hyper-relevant emails to very affected audiences, they should be sensitive to their deliverability.
Let’s look at the period between March 1 and April 21. The WHO’s spam trap hits on the Validity for Email network increased by about 20,000% during this 52-day period, more than 200 times greater than the previous 90-some days. We can confidently say 84% of these spam trap hits are from malicious actors attempting to mislead, infect (with malware), or otherwise take advantage of people by using the who.int domain, or more specifically, the donations.who.int subdomain.
Using what we know about DMARC, this seems like an obvious use case for a strict DMARC policy, right? This is the exact reason the DMARC protocol came about; to stop bad guys from abusing your domain.
There’s an important distinction to make. Those who believe DMARC can block authentic mail are not technically incorrect, at least not regarding the overarching point that DMARC reject policies cause some mail to be blocked or filtered. But surprisingly, they fail to mention another reason mail gets blocked or filtered: poor domain reputation. How does this impact the WHO?
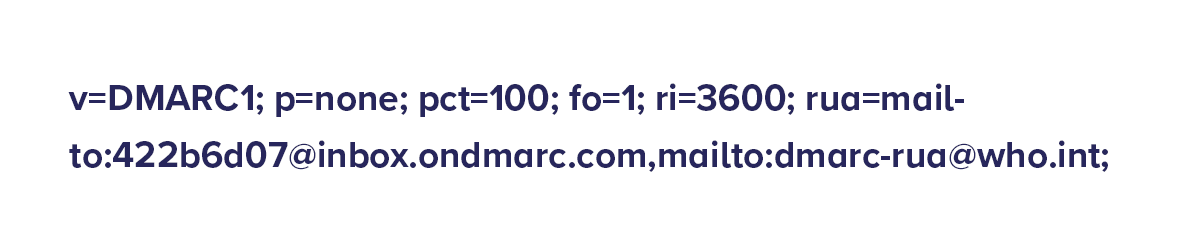
At time of writing, the WHO’s current DMARC policy is p=none, which is simply asking for reports on email messages using their domains. There is no actual enforcement or protection. This is the usual place to start when implementing DMARC, but there may be a few things to consider at this point to help reduce additional spoofing or phishing on subdomains.
Our data also shows only a small number of subdomains may be legitimate, and several others are likely spoofed, such as the unauthenticated domain donations.who.int. By adding an sp= policy at quarantine or reject at the organization domain, and managing individual p= policies for their legitimate subdomains, you can protect against a number of these attacks without having to enforce the same policy in places that may not be ready for a stricter configuration. In the case of the WHO, they are looking at massive and persistent spoofing campaigns. These phishing messages are poorly crafted and obviously bogus. They are undoubtedly generating incredible amounts of spam complaints and phishing reports, and probably have low read rates. These signals are reputation killers. If your domain starts generating higher complaint rates, bounce rates, and phishing reports out of the blue, it could easily destroy your domain reputation overnight. Imagine how many messages would end up blocked or filtered if Gmail or Hotmail decided your domain wasn’t trustworthy.
Luke Martinez
So, with that in mind, what sounds better? Tens of thousands of legitimate messages getting blocked or filtered because of your DMARC policy, or millions of malicious messages getting blocked or filtered to protect your domain reputation, which in turn protects your legitimate mail by giving it a better chance to deliver? It also protects recipients from falling victim to scams or being infected by malware because they recognize your domain.
To the credit of those arguing against a strict policy for the WHO, it is true a DMARC reject policy is not a good idea for every sender. I think the pervasiveness of the “DMARC reject hurts deliverability” sentiment is the result of too many DMARC enthusiasts blindly telling people everyone needs a reject policy, or poor implementation of the underlying SPF and DKIM authentication standards. Both are equally bad.
Determining whether a DMARC reject policy is appropriate should be taken on a case-by-case basis and should involve input from an expert. However, in situations where the domain is a high-value target for phishers and scammers, and the risk of domain reputation damage is significant, you can generally make a strong case for a reject policy.